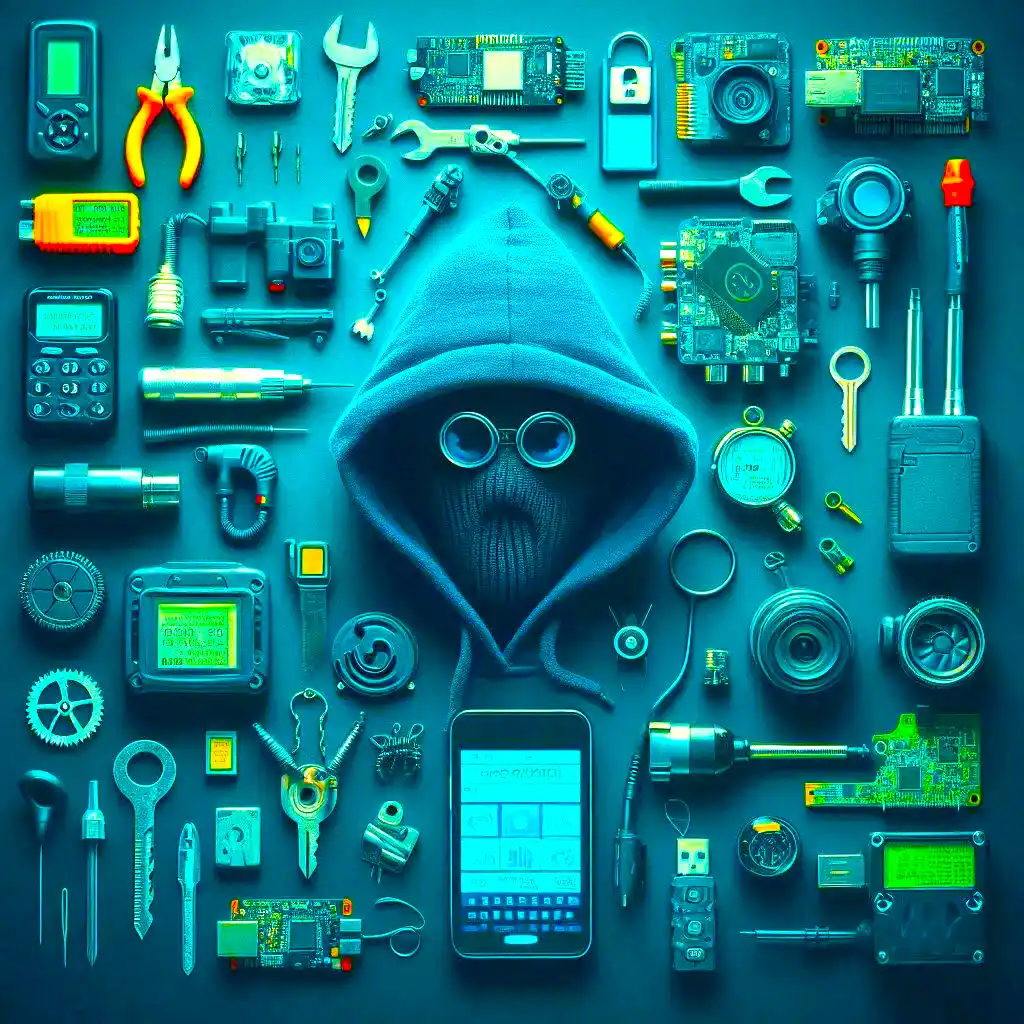
55 Deepseek Prompts for Penetration Testers: Ultimate Ethical Hacking Cheat Sheet (2025)
By Haider Mehdi, Cybersecurity Enthusiast & Penetration Tester Why Deepseek Prompts Matter in 2025 🚨 Let’s face it: penetration testing in 2025 isn’t what it […]