How To Detect Malware With Suricata Rules.
Suricata is a highly efficient, open-source, and multi-platform network security engine that incorporates advanced Intrusion Detection System (IDS), Intrusion Prevention System (IPS), and Network Security Monitoring (NSM) technologies. Developed and maintained by the Open Information Security Foundation (OISF) community since 2009, Suricata offers a comprehensive solution for detecting and preventing network security threats.
As we already explained in this article, an IDS is a passive system that is responsible for monitoring the behavior of a network to detect and report on possible unauthorized intrusions, while an IPS is an active system that works as an extension of the IDS and that , in addition to sending alerts on detections, it can also block malicious activity within the network – such as brute force attacks, DDoS, or attacks that seek to exploit vulnerabilities – and create a log with the intrusion. All this from the traffic, the file signatures, and the heuristic analysis of the flow. Additionally, IPS allows adding policies and restricting access to users and / or even applications.
That said, the most common uses for Suricata are related to scanning network traffic and analyzing traffic logs within a sandbox or sandbox environment (such as running malware). However, we can also use this tool for creating rules in order to classify malware.
Testing Meerkat
Next, we are going to see a simple example of how to use Suricata for malware classification.
Suppose we have a machine destined to perform dynamic analysis of malware samples, we could add different Suricata rules to be able to classify the type of malware that is running according to the traffic.
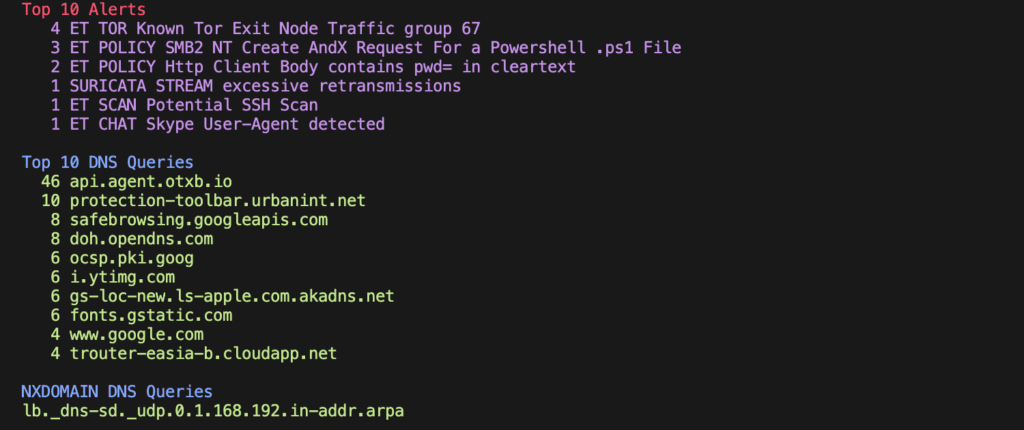
In this case, while a sample of the Trickbot banking Trojan is running on the network , a .pcap file is generated with information on the behavior of the traffic.
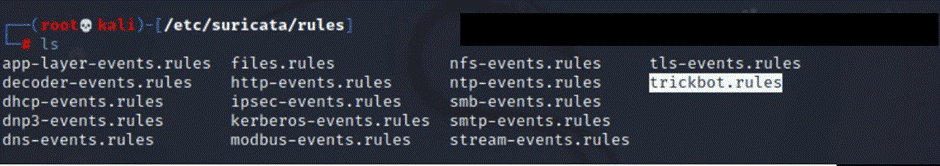
Through the network flow generated by the malware and knowing its behavior, we could create some rules in Suricata in the /etc/suricata/
rules folder :
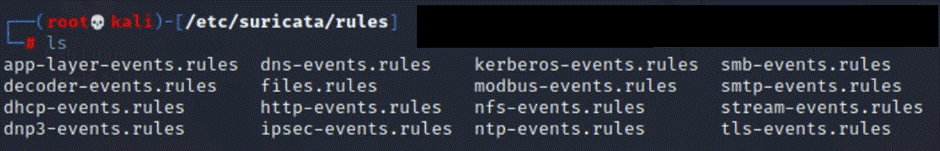
Before proceeding with the generation of the rule to detect Trickbot, we will see a short description of the basic fields to generate rules in Suricata:
| Action | Header | Rule Options |
- Action: corresponds to the action (drop, alert, etc.) that Suricata will perform when the rule is identified in the network flow.
- Header: this section corresponds to the specific network flow to be analyzed. From origin to destination. With the word “any” we can tell Meerkat that all ports will be analyzed.
- Rule: rule to implement to detect malware in our case. Within this field there are keywords that help us create our rule:
- Msg: alert message that Suricata will issue.
- flow: network flow.
- Content: contains the character string to be searched within the traffic.
- Reference: contains references, in this case we put a verification MD5 hash of a Trickbot sample.
- Sid: ID of the identified rule.
- Rev: version of the rule.
- Classtype: provides information on the classification of rules and alerts.
Taking as an example the rule for Trickbot malware, let’s proceed to add the Suricata rule in the / etc / suricata / rules directory for its detection: We save our rule for Trickbot taken from the aforementioned repository
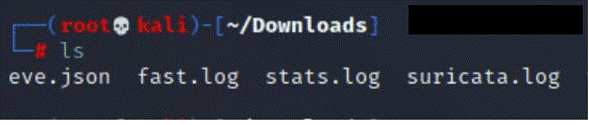
sudo suricata -c /etc/suricata/suricata.yaml -r [file.pcap]:The previous statement generates four files:
The eve.json file is the file that interests us the most at the moment, since it is the output file that provides information about alerts, anomalies, metadata, and even information about specific files and logs:
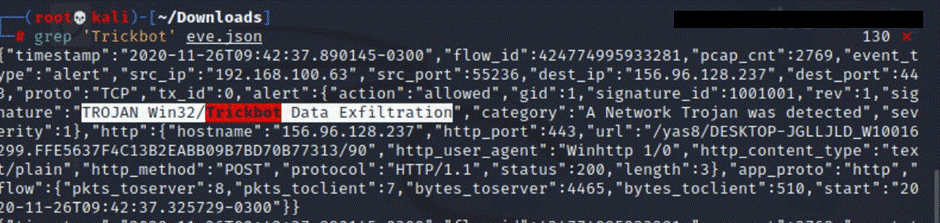
If we search for the name of the message “ Trickbot “ with the command:
grep “Trickbot” eve.jsonWe will see that our rule was able to detect the malicious file as Trickbot.
To close this proof of concept it is important to mention that Suricata is a very useful tool to perform Threat Hunting . It is capable of identifying network protocols (TPC, UDP, HTTP, ICMP, etc.) enabling real-time control of the traffic generated on our network and controlling the presence of possible malicious codes. The latter can be done through MD5 checks, as we saw in the Trickbot rule.
On the other hand, we also recommend reviewing the Suricata Open Source repository of Emerging Threats rules , where you can find rules that detect new threats.